
 The EU has once again turned its attention to domain name registration data (WHOIS) -- this time reinforcing requirements to collect, maintain, verify, and disclose WHOIS for IP enforcement purposes through its "Commission Recommendation" on measures to combat counterfeiting and enhance the enforcement of IP Rights. Published last month, this regulatory action demonstrates the EU's commitment to restore WHOIS despite... more
The EU has once again turned its attention to domain name registration data (WHOIS) -- this time reinforcing requirements to collect, maintain, verify, and disclose WHOIS for IP enforcement purposes through its "Commission Recommendation" on measures to combat counterfeiting and enhance the enforcement of IP Rights. Published last month, this regulatory action demonstrates the EU's commitment to restore WHOIS despite... more
 The U.S. Anticybersquatting Consumer Protection Act ("ACPA") is a federal law -- part of the Lanham Act that deals with trademarks and unfair competition. It says that a person can be liable if he or she registers a domain name that contains another's distinctive trademark with a bad faith intent to profit from that mark. One issue that has arisen over the years is whether registration that can give rise to liability means only the first time the domain name is registered, or whether it applies to the re-registration... more
The U.S. Anticybersquatting Consumer Protection Act ("ACPA") is a federal law -- part of the Lanham Act that deals with trademarks and unfair competition. It says that a person can be liable if he or she registers a domain name that contains another's distinctive trademark with a bad faith intent to profit from that mark. One issue that has arisen over the years is whether registration that can give rise to liability means only the first time the domain name is registered, or whether it applies to the re-registration... more
 It's incredibly hard to keep things private in the new digital age. There are far too many stories circulating about people who talked to a friend on the phone or texted about something and almost instantly got hit with ads for the subject of the conversation. And that happens without malware - no telling what information you're giving out if your devices have been infected with malicious software that is spying on you. more
It's incredibly hard to keep things private in the new digital age. There are far too many stories circulating about people who talked to a friend on the phone or texted about something and almost instantly got hit with ads for the subject of the conversation. And that happens without malware - no telling what information you're giving out if your devices have been infected with malicious software that is spying on you. more
 I've read several articles coming out of the Mobile World Congress trade show in Barcelona, Spain, and one of the common threads is that there was a lot of talk about 5.5G (or 5G Advanced) - the next iteration of 5G. My first question on reading about this was to ask what new features are being discussed that were not part of the original announced promises of 5G. I went back and read a few of my blogs and other articles that were written when 5G was first announced. more
I've read several articles coming out of the Mobile World Congress trade show in Barcelona, Spain, and one of the common threads is that there was a lot of talk about 5.5G (or 5G Advanced) - the next iteration of 5G. My first question on reading about this was to ask what new features are being discussed that were not part of the original announced promises of 5G. I went back and read a few of my blogs and other articles that were written when 5G was first announced. more
 On 29 March 2024, an announcement was posted notifying the world that the Open-Source Software (OSS) package "xz-utils," which includes the xz data compression program and a library of software routines called "liblzma" and which is present in most Linux distributions, had been compromised. The insertion of the compromised code was done by "Jia Tan", the official maintainer of the xz-utils package. more
On 29 March 2024, an announcement was posted notifying the world that the Open-Source Software (OSS) package "xz-utils," which includes the xz data compression program and a library of software routines called "liblzma" and which is present in most Linux distributions, had been compromised. The insertion of the compromised code was done by "Jia Tan", the official maintainer of the xz-utils package. more
 During CSG Open Working Session at ICANN79, Members from the ICANN Community were invited to an open meeting to share their experiences with Registration Data Request System (RDRS) from the Requestor side. As President of the Edgemoor Research Institute (ERI), I had the honor to present the keynote address and I am pleased to be able to provide you with ERI's report of the meeting. more
During CSG Open Working Session at ICANN79, Members from the ICANN Community were invited to an open meeting to share their experiences with Registration Data Request System (RDRS) from the Requestor side. As President of the Edgemoor Research Institute (ERI), I had the honor to present the keynote address and I am pleased to be able to provide you with ERI's report of the meeting. more
 In the digital era's transformative landscape, the intersection of Internet Governance and Sustainable Development emerges as a focal point for global discourse. It is widely recognized that the Internet, in its vast potential, holds the key to unlocking solutions for many of the challenges we face. However, this potential could be significantly underutilized, or worse, lead to adverse effects without a robust governance framework. more
In the digital era's transformative landscape, the intersection of Internet Governance and Sustainable Development emerges as a focal point for global discourse. It is widely recognized that the Internet, in its vast potential, holds the key to unlocking solutions for many of the challenges we face. However, this potential could be significantly underutilized, or worse, lead to adverse effects without a robust governance framework. more
 In 2021, the story was price. In 2022, the story was price and large block supply. The story in 2023 is decline -- but with a notable caveat. Spurred by unprecedented unit pricing, the North American IPv4 market in 2022 experienced its second-best year in terms of overall traded volume, and in both 2022 and in 2023, large block market activity was as robust as ever, with sellers trading large blocks at over $50 per number. more
In 2021, the story was price. In 2022, the story was price and large block supply. The story in 2023 is decline -- but with a notable caveat. Spurred by unprecedented unit pricing, the North American IPv4 market in 2022 experienced its second-best year in terms of overall traded volume, and in both 2022 and in 2023, large block market activity was as robust as ever, with sellers trading large blocks at over $50 per number. more
 The most contentious issue throughout negotiations was that of scope—whether the Convention would cover the private sector at all, and if so, to what extent. Leaks of the negotiations and commentary by journalists indicate that several states, primarily the United States, were keen to see the Convention not directly applying to private entities. more
The most contentious issue throughout negotiations was that of scope—whether the Convention would cover the private sector at all, and if so, to what extent. Leaks of the negotiations and commentary by journalists indicate that several states, primarily the United States, were keen to see the Convention not directly applying to private entities. more
 Today's blog talks about a critical part of the broadband network that most people don't know about -- carrier hotels. These are locations that have been created for the specific purpose of allowing carriers to connect to each other. The need for carrier hotels became apparent in the year after the passage of the Telecommunications Act of 1996. That new law allowed local competition for telephone service. more
Today's blog talks about a critical part of the broadband network that most people don't know about -- carrier hotels. These are locations that have been created for the specific purpose of allowing carriers to connect to each other. The need for carrier hotels became apparent in the year after the passage of the Telecommunications Act of 1996. That new law allowed local competition for telephone service. more
 The unveiling of the Global Digital Compact's (GDC) zero draft on April 1, 2024, heralds a critical juncture in the quest to frame a digital future that is equitable, secure, and human-centered. Orchestrated under the leadership of UN Secretary-General António Guterres, the initiative endeavors to forge a consensus-driven framework for global digital cooperation. more
The unveiling of the Global Digital Compact's (GDC) zero draft on April 1, 2024, heralds a critical juncture in the quest to frame a digital future that is equitable, secure, and human-centered. Orchestrated under the leadership of UN Secretary-General António Guterres, the initiative endeavors to forge a consensus-driven framework for global digital cooperation. more
 The IPv4 market has created serious interest in the protocol far beyond the natural confines of networking professionals. These assets are worth a lot. Marketplaces, IPv4.Global's especially, have grown to be large centers of asset transfer by buyers and sellers of IPv4 addresses. IPv4.Global has helped transfer over $1 billion in IPv4 blocks. more
The IPv4 market has created serious interest in the protocol far beyond the natural confines of networking professionals. These assets are worth a lot. Marketplaces, IPv4.Global's especially, have grown to be large centers of asset transfer by buyers and sellers of IPv4 addresses. IPv4.Global has helped transfer over $1 billion in IPv4 blocks. more
 During the ICANN79 in San Juan, Puerto Rico, in March 2024, the North America School of Internet Governance (NASIG 2024) convened with an over-encompassing theme, "Confronting Truth, Trust, and Hope in Internet Governance." A pivotal panel discussion titled "Can We Survive Digital Fragmentation?" underscored the essentiality of global connectivity and the urgency to understand and address the layers of fragmentation impacting the internet's universal fabric. more
During the ICANN79 in San Juan, Puerto Rico, in March 2024, the North America School of Internet Governance (NASIG 2024) convened with an over-encompassing theme, "Confronting Truth, Trust, and Hope in Internet Governance." A pivotal panel discussion titled "Can We Survive Digital Fragmentation?" underscored the essentiality of global connectivity and the urgency to understand and address the layers of fragmentation impacting the internet's universal fabric. more
 Eight countries in West Africa reported Internet outages after damage was reported to four different undersea fiber cables. The most affected countries are Ivory Coast, Liberia, and Benin, with additional problems caused in Ghana, Nigeria, and Cameroon. Lesser impact was felt in South Africa, Senegal, and Portugal. There has been no official word on what caused the problem, but it's likely due to the shifting of the seabed due to seismic activity. more
Eight countries in West Africa reported Internet outages after damage was reported to four different undersea fiber cables. The most affected countries are Ivory Coast, Liberia, and Benin, with additional problems caused in Ghana, Nigeria, and Cameroon. Lesser impact was felt in South Africa, Senegal, and Portugal. There has been no official word on what caused the problem, but it's likely due to the shifting of the seabed due to seismic activity. more
 Sixty years ago, Paul Baran and Sharla Boehm at The RAND Corporation released a seminal paper that would fundamentally reshape the cyber world forever more. Their paper, simply known as Memorandum RM -- 1303, described how specialized computers could be used to route digital communications among a distributed universe of other computers. It set the stage for a flood of endless developments that resulted in the interconnected world of everything, everywhere, all the time. more
Sixty years ago, Paul Baran and Sharla Boehm at The RAND Corporation released a seminal paper that would fundamentally reshape the cyber world forever more. Their paper, simply known as Memorandum RM -- 1303, described how specialized computers could be used to route digital communications among a distributed universe of other computers. It set the stage for a flood of endless developments that resulted in the interconnected world of everything, everywhere, all the time. more
In response to ongoing controversies over the use of copyrighted content in training artificial intelligence, U.S. Representative Adam Schiff has introduced the Generative AI Disclosure Act more
Major U.S. broadband providers are now mandated to display clear consumer labels outlining prices, speeds, and data allowances for their services. This directive from the Federal Communications Commission (FCC) applies to all major standalone home and mobile broadband plans, targeting providers with over 100,000 subscribers. more
In a landmark move that may pave the way for enhanced online data protection in the United States, key congressional committee leaders are on the brink of finalizing a national framework to safeguard Americans' personal data on the Internet. more
 Scientists Set New Internet Speed World Record: 4.5 Million Times Faster Than Average Broadband
Scientists Set New Internet Speed World Record: 4.5 Million Times Faster Than Average Broadband
In a groundbreaking development, scientists from Aston University, in collaboration with the National Institute of Information and Communications Technology in Japan and Nokia Bell Labs in the US, have set a new world record in internet speed. more
The Internet Corporation for Assigned Names and Numbers (ICANN) has unveiled the first cycle of its Grant Program, earmarking up to $10 million for projects aimed at enhancing Internet resilience and global interoperability. more
 Biden Administration Alerts Governors to Rising Cyber Threats on U.S. Water Systems
Biden Administration Alerts Governors to Rising Cyber Threats on U.S. Water Systems
The Biden administration has issued a stark warning to the nation's governors about the increasing threat of cyberattacks on the United States' water and wastewater systems. more
The U.S. Federal Communications Commission (FCC) has updated the national broadband speed standard to at least 100Mbps download and 20Mbps upload speeds, marking the first adjustment since January 2015. more
The Council of European National Top-level domain Registries (CENTR) has issued recommendations to modify the EU's Financial Data Access Regulation proposal, warning about the potentially irreversible effects on European consumers and businesses. more
Multiple subsea cable breaks have significantly disrupted internet connectivity across South Africa, affecting a wide range of internet and cloud service providers and leaving thousands of users disconnected. more
 Ransomware Crisis in U.S. Healthcare
Ransomware Crisis in U.S. Healthcare
A significant ransomware attack by a group known as AlphV or BlackCat has severely disrupted pharmacies across the U.S., affecting the delivery of prescription medications for over ten days. This attack on Change Healthcare has resulted in considerable difficulties for hospital pharmacies and nationwide drug distribution. more
The CENTR Global TLD Report 2024 highlights a modest growth in registered domains across the EU, with a notable increase in Poland, France, and Italy, primarily through their national ccTLDs. more
The United States, along with key global partners, has formally committed to principles guiding the development of 6G technology, as announced by the White House. This move comes amidst a strategic contest to shape the future of wireless communication standards, driven by concerns over authoritarian regimes exerting greater control over the internet within their borders. more
A series of underwater communications cables connecting Saudi Arabia and Djibouti have been rendered inoperative, an incident attributed to the actions of Yemen's Houthi rebels. This revelation comes from an exclusive report by the Israeli news outlet, Globes. more
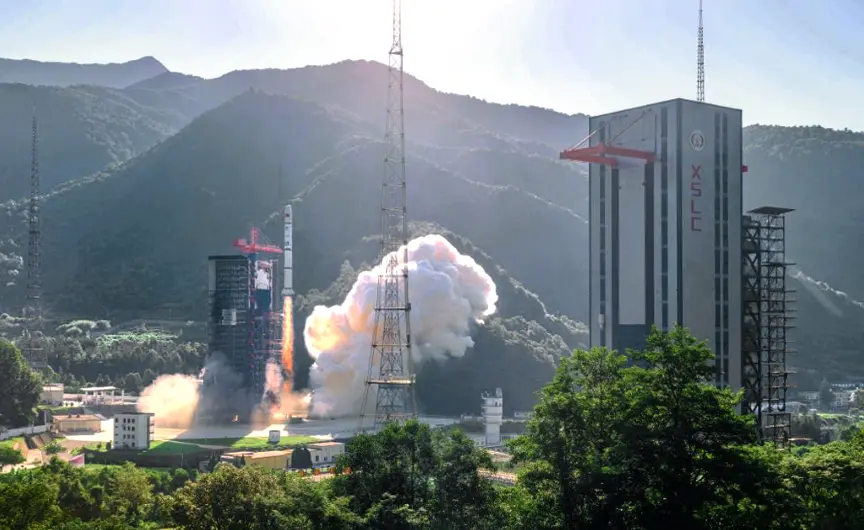 China’s Satellite Internet Ambitions: A Quest to Rival SpaceX
China’s Satellite Internet Ambitions: A Quest to Rival SpaceX
China launched a notable 67 commercial rockets in a single year, marking a significant effort to catch up with the United States, which led with 116 launches, primarily for SpaceX's Starlink project. more
In a recently released paper by the Council of European National Top-level Domain Registries (CENTR), authored in collaboration with Chris Buckridge, the spotlight is once again on the multistakeholder approach to Internet governance. more
 Global Law Enforcement Strikes Major Blow Against LockBit Ransomware Operation
Global Law Enforcement Strikes Major Blow Against LockBit Ransomware Operation
In a significant global operation, law enforcement agencies from 10 countries have severely disrupted the LockBit ransomware group, recognized as the most prolific and harmful cyber threat worldwide. more
In a significant service disruption early Thursday, AT&T's network experienced widespread outages, affecting cellular service and internet connectivity for users across the United States. According to the tracking site Downdetector, the issues began around 4 a.m. ET, with over 32,000 reports of outages, which surged to more than 71,000 by 8 a.m. ET. more
As governments convene to discuss the UN Cybercrime Treaty, Google is urging caution, warning that the current draft could endanger online security and free expression. more
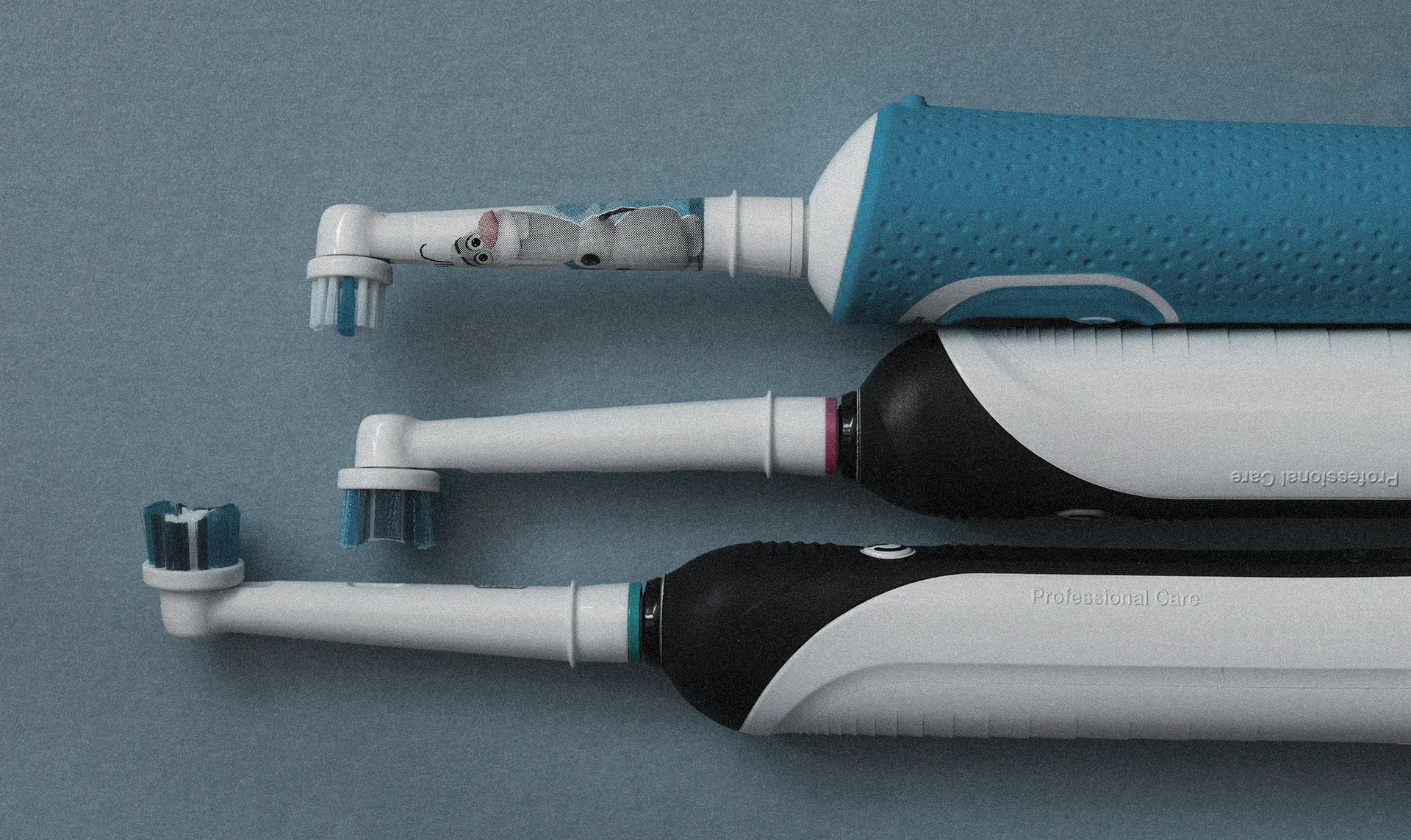 Millions of Smart Toothbrushes Hijacked in Cyberattack on Swiss Firm
Millions of Smart Toothbrushes Hijacked in Cyberattack on Swiss Firm
Hackers have commandeered approximately three million smart toothbrushes, transforming them into a botnet for launching a DDoS (Distributed Denial of Service) attack against a Swiss company's website, causing significant financial losses. more
The U.S. has introduced a new visa restriction policy targeting individuals implicated in the misuse of commercial spyware. Secretary of State Antony Blinken announced that these restrictions would apply to those involved in, facilitating, or benefiting from the abuse of such technology. more
Sponsored byCSC

Sponsored byIPv4.Global

Sponsored byWhoisXML API

Sponsored byRadix

Sponsored byDNIB.com

Sponsored byVerisign

Sponsored byVerisign

 After analyzing 21+ million newly registered domains (NRDs) added from 1 January to 31 March 2024, our researchers found that the new domain registration volume declined by about 32% from the previous quarter. more
After analyzing 21+ million newly registered domains (NRDs) added from 1 January to 31 March 2024, our researchers found that the new domain registration volume declined by about 32% from the previous quarter. more
 Threat actors have been abusing App Installer, a Windows 10 feature that makes installing applications more convenient. The abuse could lead to ransomware distribution and was likely carried out by financially motivated actors Storm-0569, Storm-1113, Sangria Tempest, and Storm-1674. more
Threat actors have been abusing App Installer, a Windows 10 feature that makes installing applications more convenient. The abuse could lead to ransomware distribution and was likely carried out by financially motivated actors Storm-0569, Storm-1113, Sangria Tempest, and Storm-1674. more
 macOS has been gaining the unwanted attention of more and more backdoor operators since late 2023. In February 2024, Bitdefender uncovered RustDoor, which was written in Rust and possibly has ties to the operators of a Windows ransomware. more
macOS has been gaining the unwanted attention of more and more backdoor operators since late 2023. In February 2024, Bitdefender uncovered RustDoor, which was written in Rust and possibly has ties to the operators of a Windows ransomware. more
 Group-IB uncovered ResumeLooters, a threat actor group specializing in victimizing job hunters to steal their personally identifiable information (PII). more
Group-IB uncovered ResumeLooters, a threat actor group specializing in victimizing job hunters to steal their personally identifiable information (PII). more
 In the past two decades, at least 41 advanced persistent threat (APT) groups have launched attacks on entities and organizations based in North America. more
In the past two decades, at least 41 advanced persistent threat (APT) groups have launched attacks on entities and organizations based in North America. more
 The Citizen Lab recently uncovered an ongoing online propaganda campaign they have dubbed "PAPERWALL" that has been targeting local news outlets across 30 countries in Europe, Asia, and Latin America. more
The Citizen Lab recently uncovered an ongoing online propaganda campaign they have dubbed "PAPERWALL" that has been targeting local news outlets across 30 countries in Europe, Asia, and Latin America. more
 The passage provided features an interview with Chad Silverstein and Jack Hazan, who is the Executive Vice President at Hilco Streambank. Hazan oversees the operations of Hilco’s IPv4.Global business division. more
The passage provided features an interview with Chad Silverstein and Jack Hazan, who is the Executive Vice President at Hilco Streambank. Hazan oversees the operations of Hilco’s IPv4.Global business division. more
 VexTrio, a traffic distribution system (TDS) provider believed to be an affiliate of ClearFake and SocGholish, among other threat actors, has been active since 2017. more
VexTrio, a traffic distribution system (TDS) provider believed to be an affiliate of ClearFake and SocGholish, among other threat actors, has been active since 2017. more
 In the past, DarkGate attacks were either lumped together with or classified as BattleRoyal remote access Trojan (RAT) attacks. Recent evidence, however, showed the two malware are not one and the same. more
In the past, DarkGate attacks were either lumped together with or classified as BattleRoyal remote access Trojan (RAT) attacks. Recent evidence, however, showed the two malware are not one and the same. more
 Among the latest to suffer from zero-day exploitation is Ivanti, a software company providing endpoint management and remote access solutions to various organizations, including U.S. federal agencies. more
Among the latest to suffer from zero-day exploitation is Ivanti, a software company providing endpoint management and remote access solutions to various organizations, including U.S. federal agencies. more
 Law enforcement agencies shut down xDedic, a cybercrime-as-a-service (CaaS) marketplace specifically providing web servers to cybercriminals, back in 2019. However, WhoisXML API threat researcher Dancho Danchev posits that parts of its backend infrastructure may remain traceable. more
Law enforcement agencies shut down xDedic, a cybercrime-as-a-service (CaaS) marketplace specifically providing web servers to cybercriminals, back in 2019. However, WhoisXML API threat researcher Dancho Danchev posits that parts of its backend infrastructure may remain traceable. more
 New kids on the cybercrime block, pig butchering scams, have been making waves lately, and it is not surprising why. Scammers have been earning tons from them by being able to trick users into investing in seemingly legitimate business ventures but losing their hard-earned cash instead. more
New kids on the cybercrime block, pig butchering scams, have been making waves lately, and it is not surprising why. Scammers have been earning tons from them by being able to trick users into investing in seemingly legitimate business ventures but losing their hard-earned cash instead. more
 In the digital age, where every device, from smartphones to fridges, connects to the Internet, the topic of IP addresses becomes increasingly relevant. An IP address, a unique identifier for devices on the Internet, has seen its fair share of evolution from IPv4 to IPv6. Yet, the question lingers: Are unused IPv4 addresses a hidden treasure? more
In the digital age, where every device, from smartphones to fridges, connects to the Internet, the topic of IP addresses becomes increasingly relevant. An IP address, a unique identifier for devices on the Internet, has seen its fair share of evolution from IPv4 to IPv6. Yet, the question lingers: Are unused IPv4 addresses a hidden treasure? more
 RisePro, a malware-as-a-service data stealer, has been plaguing users since 2022. ANY.RUN recently discovered and analyzed its latest version in great depth and identified 10 indicators of compromise (IoCs) -- three domains and seven IP addresses. more
RisePro, a malware-as-a-service data stealer, has been plaguing users since 2022. ANY.RUN recently discovered and analyzed its latest version in great depth and identified 10 indicators of compromise (IoCs) -- three domains and seven IP addresses. more